The Complete Guide to Tackling Symfony Development Obstacles
Symfony is a powerful and reusable PHP component with high modularity compared to Laravel. This causes a steeper learning curve but results in a reliable web application.
As a new developer, facing challenges while working with Symfony leads to bottlenecks. This is where the experience of the Symfony web development company comes in.
Through the medium of this guide, we will steer you through some common obstacles while working with the Symfony framework.
Vulnerabilities of Symfony
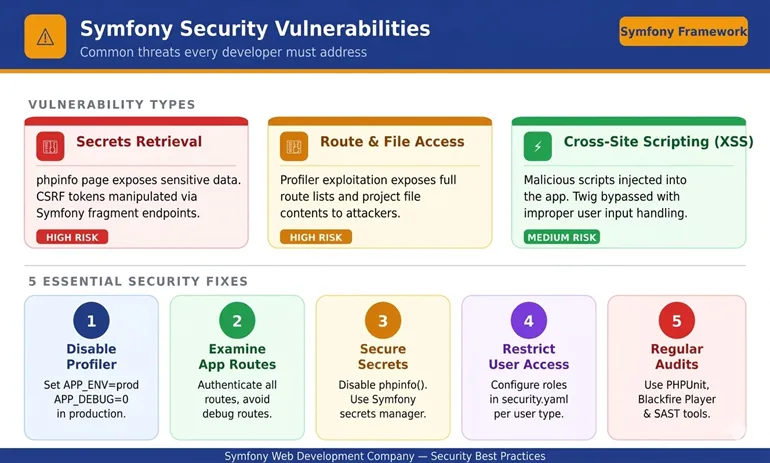
Like any other framework, Symfony does have certain limitations and security vulnerabilities. Profiler exposes several vulnerabilities that underscore its seriousness.
-
Retrieving Secrets
The phpinfo page enables attackers to retrieve sensitive information, and when compromised, the dataset can easily be manipulated. Another concern lies within the Symfony fragments, with which a malicious actor can forge requests and also manipulate CSRF tokens.
-
Accessing the Route List and Reading Files
An attacker can easily access the route list of the application by exploiting the profiler on the request return. And with a valid path line and a specific starting point, the content of the project can also be accessed.
-
Cross-Site Scripting XSS
Cross-site scripting is a common form of attack that affects the web application by injecting malicious scripts. Even with the protection of Twig automation, improper handling of user inputs leads to an XSS attack.
And due to these underlying factors, partnering with the Symfony web development company becomes pivotal.
How to Tackle Such Vulnerabilities?
Well, one of the best precaution is to take is never to share the Symfony Profiler publicly. Moreover, EOS (Enemies of Symfony) can be incorporated to automate these exploits.
Symfony toolbar enables developers to determine whether the application is compromised or not.
- Deactivate profiler and toolbar: You can deactivate the toolbar and profiler by setting APP_ENV=prod and APP_DEBUG=0. The toolbar and profiler might be necessary during the development stage, but during the production stage, they might be vulnerable.
- Examine the App Route: What every professional Symfony web development company follows is a strict examination of the app route to check if access to the profiler is authorized. The best practice is to implement authentication and avoid activating the debug or test route.
- Securing Sensitive Information: API keys, database, and environment variables are the backbone of the project and should never be revealed. To safeguard them, disable phpinfo() and store secrets securely using the Symfony secrets management system.
- Restrict Access as Per User: One of the common practices you can adhere to is restricting access as per the role and user. Configure the config/package/security.yaml file, defining the configuration.
- Regular Security Checks and Audit: Many novice developers ignore the significance of regular security checks and audits. Developers have to keep the Symfony and dependencies on check, run regular scans, and leverage third-party scanners.
Apart from these incorporation certain fixes can be made in terms of user aspects. It includes preserving the access right to specific resources, preventing IDOR vulnerability.
The best part is that Symfony offers tools to prevent such right of access, which adds a constraint right to the access path.
Best Practices for Symfony Development
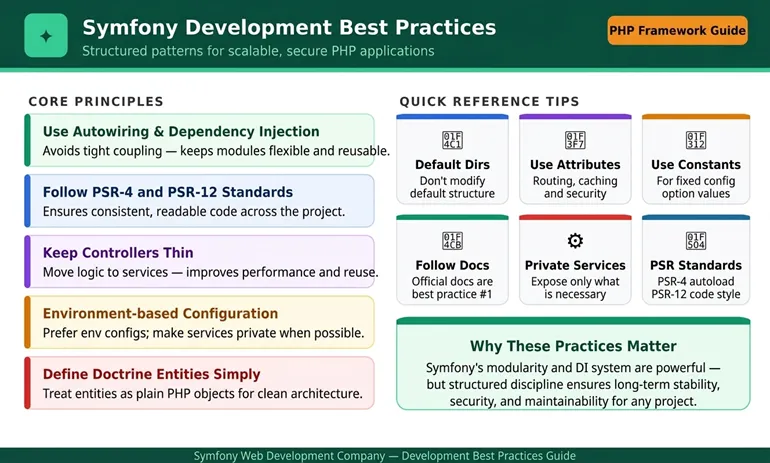
Probably the best practice for any framework is to adhere to the documentation.
The entire framework operates on the Dependency Injection (DI) and autowiring that makes the module highly modular and loosely coupled.
So, here are some similar concepts that should be incorporated by adhering with Symfony.
- Use autowiring and avoid tigh coupling to maintain the flexibility of the framework.
- Follow PSR-4 and PSR-12 code standard to ensure the application remains readable.
- Keep the controller thin unlike Laravel. It ensures better performance and promotes reusability.
- Don’t mess with the default directory, as it provides the most effective results in application.
- For certain configuration options that remains unchanged, sue constant.
- Use attributes to configure routing, caching, and security.
- Prefer environment based configuration and make service private whenever possible.
- Define the Doctrine entities as they are simple PHP objects.
By enforcing such practices for your Symfony development you are basically subscribing to the structured and secure approach.
If your project needs lean toward Python-based frameworks, working with the best Django web development company can give you solutions that are just as efficient, safe, and scalable, and that are made for modern development needs.
Final Words
This guide have extensively discussed about all the elements that needs to be taken into account for concise deployment. As a novice developer the above mentioned vulnerabilities to taken care and best practices is directly endorsed by a professional Symfony web development company.
Meanwhile, to the businesses that consider the Python-based solutions, the selection of the most appropriate Best Django development company can provide equally powerful, safe, and scalable results that fit the contemporary development requirements.
Finally, the appropriate skills such as Symphony and Django can be significant to turn the development issues into the success in the long-run.
FAQs
Is Symfony recommended for enterprise-level use?
Absolutely! Symfony is widely used among enterprises, integrated with features like CSRF protection, authentication, and input validation.
Why is it recommended not to use the Symfony Profiler during production?
Symfony Profiler consists of detailed information about requests, routes, and configuration, which provides all the detailed information to an attacker.
What tools can be used for Symfony security testing?
You can use various built-in and third-party tools, like PHPUnit, SecurityBundle, and Symfony Panther. And for third-party tools, you can rely on Blackfire Player, SAST, and Behat.
Are Symfony fragments a security risk?
Yes, Symfony fragments can pose a security threat if not secured. It acts as a threat as it provides access to restricted content and manipulates data.